Requirements
The ingestion also works with Superset 2.0.0 🎉 API Connection: To extract metadata from Superset via API, user must have at leastcan read on Chart & can read on Dashboard permissions.
Database Connection: To extract metadata from Superset via MySQL or Postgres database, database user must have at least SELECT privilege on dashboards & slices tables within superset schema.
Metadata Ingestion
Connection Details
Connection Details
- Host and Port: The
Host and Postparameter is common for all three modes of authentication which specifies the host and port of the Superset instance. This should be specified as a string in the formathttp://hostname:portorhttps://hostname:port. For example, you might set the hostPort parameter tohttps://org.superset.com:8088. - Superset Connection: Add the connection details to fetch metadata from Superset either through APIs or Database.
For Superset API Connection
Superset API connection is the default mode of authentication where we fetch the metadata using Superset APIs.- Username: Username to connect to Superset, for ex.
user@organization.com. This user should have access to relevant dashboards and charts in Superset to fetch the metadata. - Password: Password of the user account to connect with Superset.
- Provider: Choose between
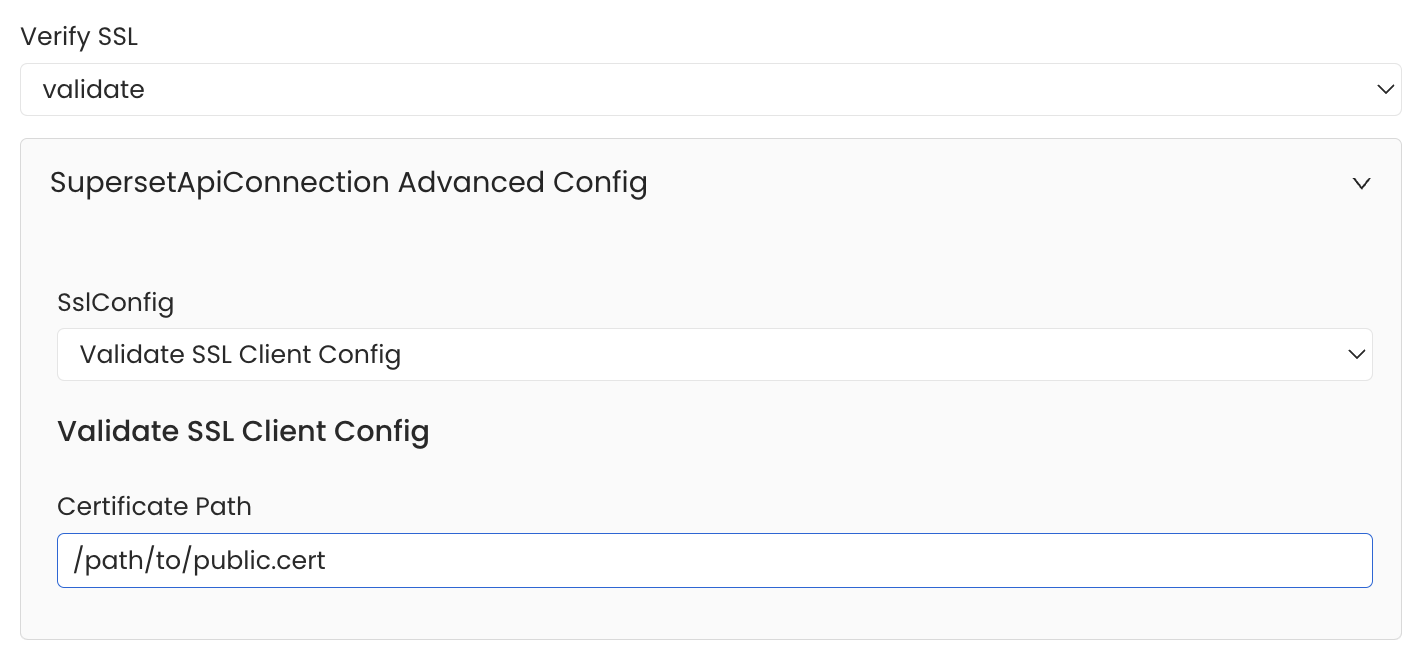
db(default) orldapmode of Authentication provider for the Superset service. This parameter is used internally to connect to Superset’s REST API. - Verify SSL:
Client SSL verification. Make sure to configure the SSLConfig if enabled.
Possible values:
validate: Validate the certificate using the public certificate (recommended).ignore: Ignore the certification validation (not recommended for production).no-ssl: SSL validation is not needed.
- SSL Config: Client SSL configuration in case we are connection to a host with SSL enabled.
- Certificate Path: CA certificate path in the instance where the ingestion run. E.g.,
/path/to/public.cert. Will be used if Verify SSL is set tovalidate. For MySQL Connection You can use Mysql Connection when you have SSO enabled and your Superset is backed by Mysql database. - Username: Specify the User to connect to MySQL. It should have enough privileges to read all the metadata. Make sure the user has select privileges on
dashboards,tables&slicestables of superset schema. - Password: Password to connect to MySQL.
- Host and Port: Enter the fully qualified hostname and port number for your MySQL deployment in the Host and Port field.
- databaseSchema: Enter the database schema which is associated with the Superset instance.
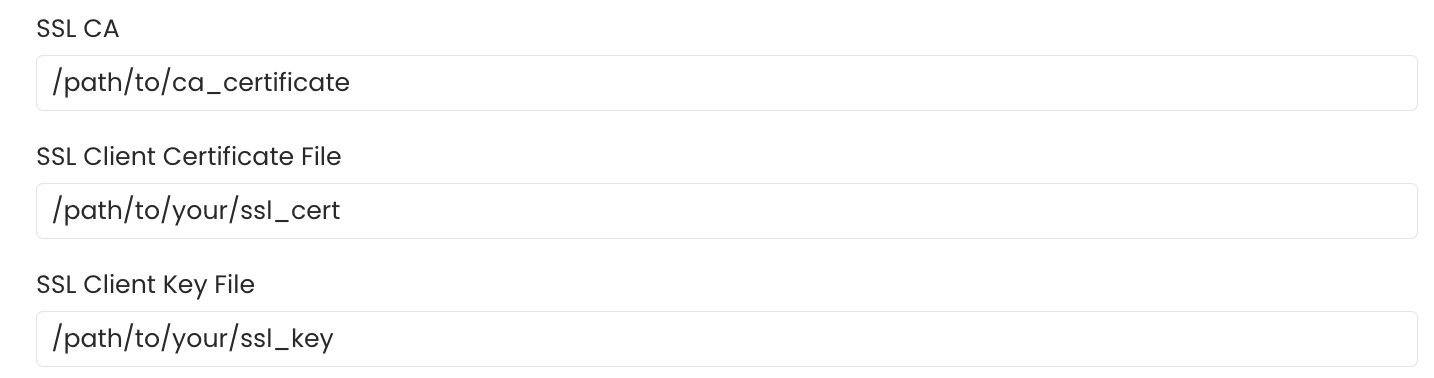
- caCertificate: Provide the path to ssl ca file.
- sslCertificate: Provide the path to ssl client certificate file (ssl_cert).
- sslKey: Provide the path to ssl client certificate file (ssl_key).
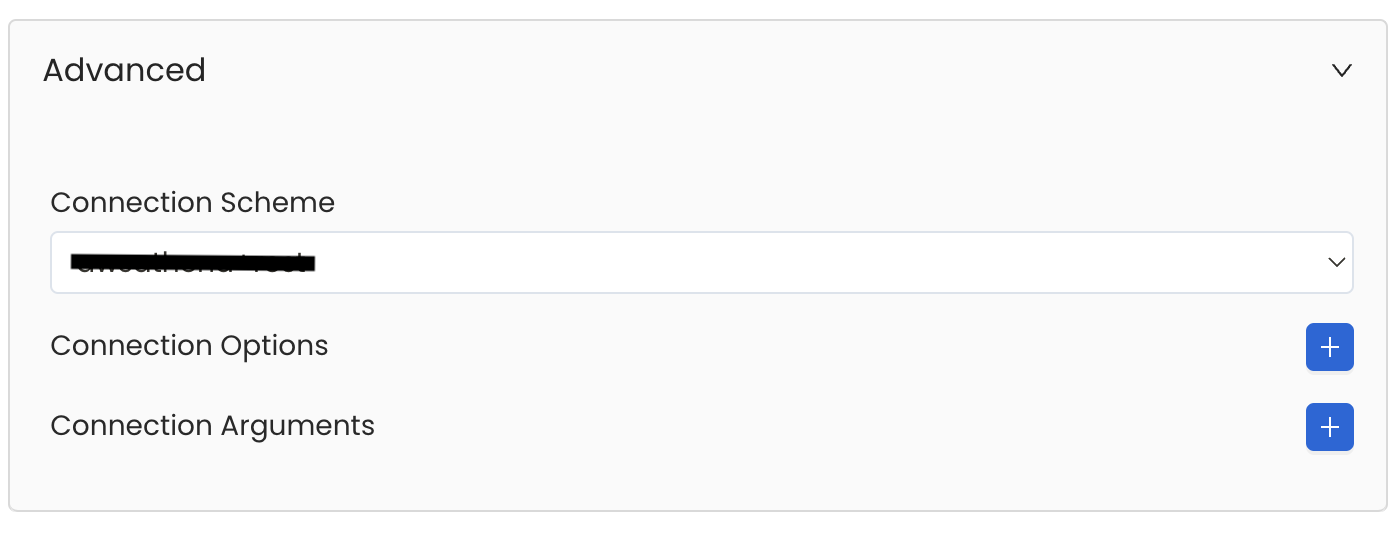
Advanced Configuration
Database Services have an Advanced Configuration section, where you can pass extra arguments to the connector
and, if needed, change the connection Scheme.This would only be required to handle advanced connectivity scenarios or customizations.
- Connection Options (Optional): Enter the details for any additional connection options that can be sent to database during the connection. These details must be added as Key-Value pairs.
-
Connection Arguments (Optional): Enter the details for any additional connection arguments such as security or protocol configs that can be sent during the connection. These details must be added as Key-Value pairs.
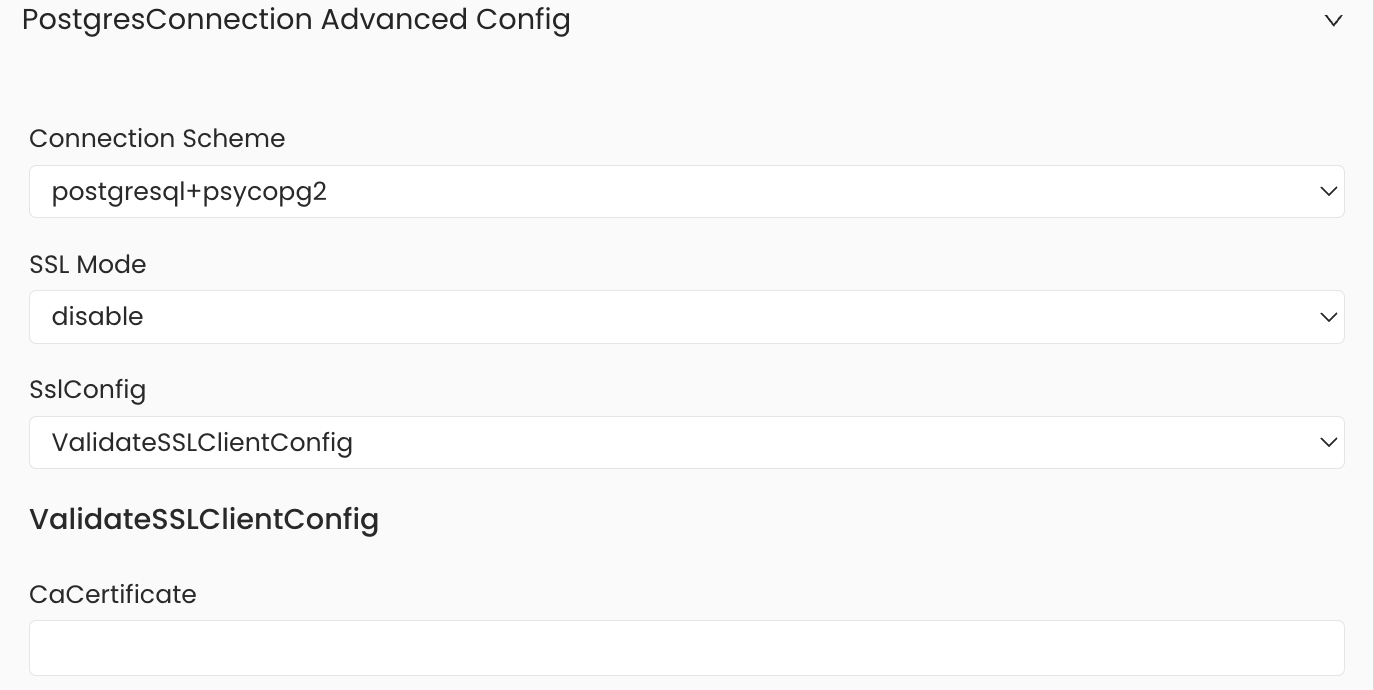
For Postgres Connection
You can use Postgres Connection when you have SSO enabled and your Superset is backed by Postgres database.
- Username: Specify the User to connect to Postgres. Make sure the user has select privileges on
dashboards,tables&slicestables of superset schema. - Password: Password to connect to Postgres.
- Host and Port: Enter the fully qualified hostname and port number for your Postgres deployment in the Host and Port field.
- Database: Initial Postgres database to connect to. Specify the name of database associated with Superset instance.
- caCertificate: Provide the path to ssl ca file.
Advanced Configuration
Database Services have an Advanced Configuration section, where you can pass extra arguments to the connector
and, if needed, change the connection Scheme.This would only be required to handle advanced connectivity scenarios or customizations.
- Connection Options (Optional): Enter the details for any additional connection options that can be sent to database during the connection. These details must be added as Key-Value pairs.
-
Connection Arguments (Optional): Enter the details for any additional connection arguments such as security or protocol configs that can be sent during the connection. These details must be added as Key-Value pairs.
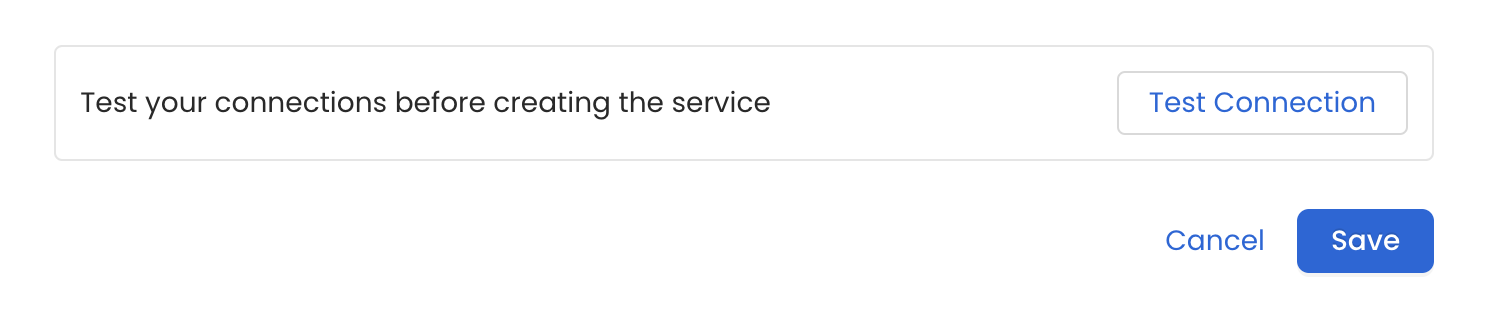
Test the Connection
Once the credentials have been added, click on Test Connection and Save the changes.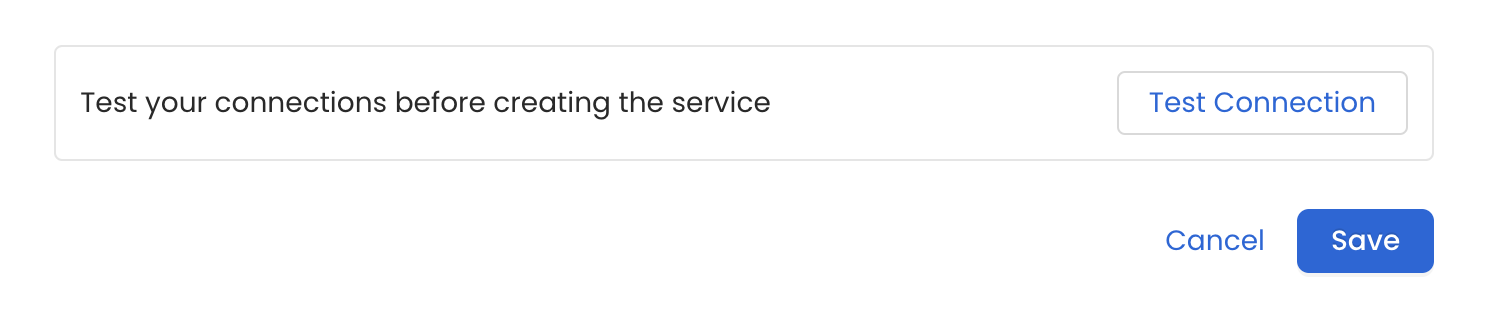
Configure Metadata Ingestion
In this step we will configure the metadata ingestion pipeline,
Please follow the instructions below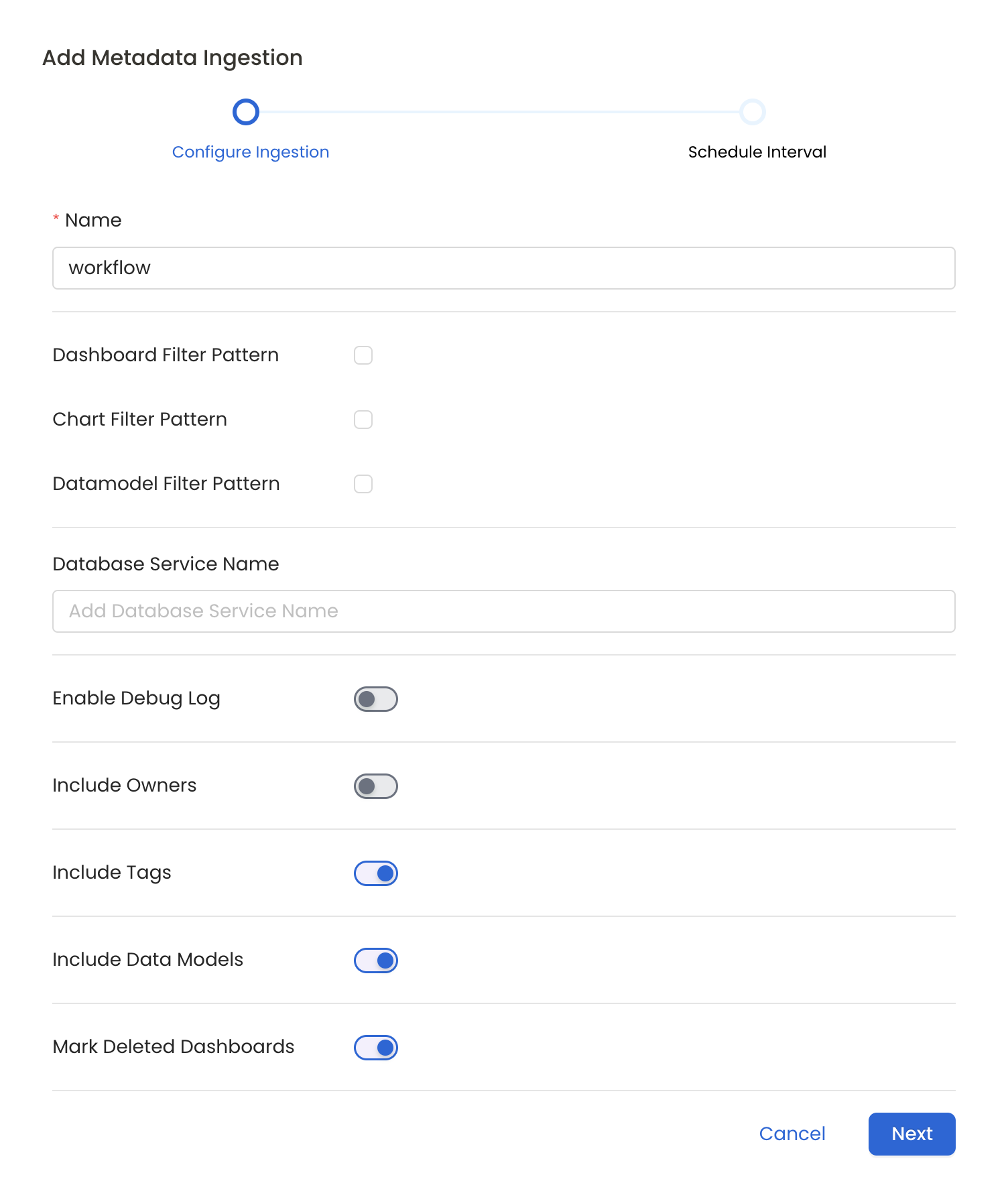
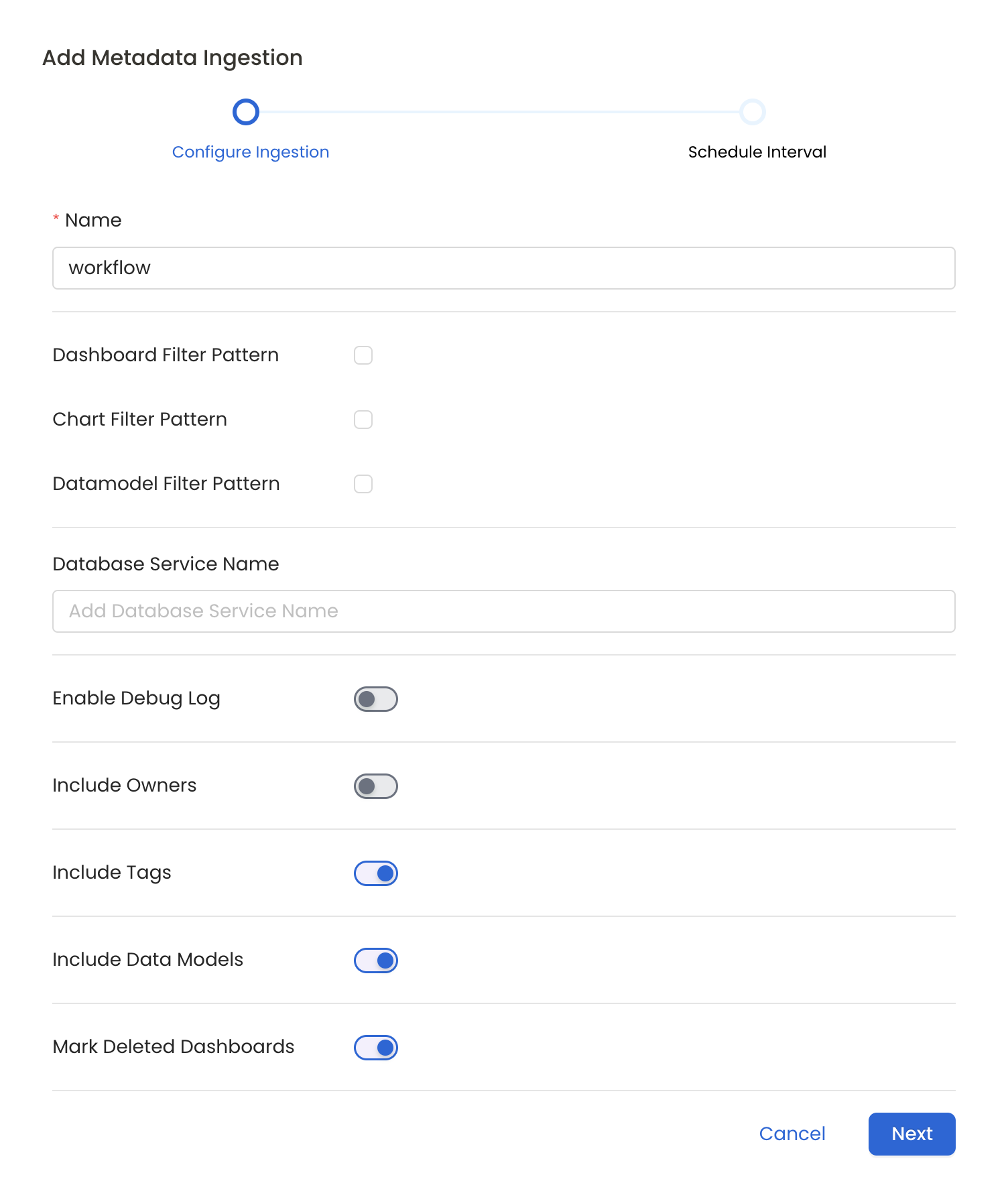
Metadata Ingestion Options
- Name: This field refers to the name of ingestion pipeline, you can customize the name or use the generated name.
- Dashboard Filter Pattern (Optional): Use it to control whether to include dashboard as part of metadata ingestion.
- Include: Explicitly include dashboards by adding a list of comma-separated regular expressions to the ‘Include’ field. OpenMetadata will include all dashboards with names matching one or more of the supplied regular expressions. All other dashboards will be excluded.
- Exclude: Explicitly exclude dashboards by adding a list of comma-separated regular expressions to the ‘Exclude’ field. OpenMetadata will exclude all dashboards with names matching one or more of the supplied regular expressions. All other dashboards will be included.
- projectFilterPattern: Filter the dashboards, charts and data sources by projects. Note that all of them support regex as include or exclude. E.g., “My project, My proj.*, .*Project”.
- Chart Pattern (Optional): Use it to control whether to include charts as part of metadata ingestion.
- Include: Explicitly include charts by adding a list of comma-separated regular expressions to the ‘Include’ field. OpenMetadata will include all charts with names matching one or more of the supplied regular expressions. All other charts will be excluded.
- Exclude: Explicitly exclude charts by adding a list of comma-separated regular expressions to the ‘Exclude’ field. OpenMetadata will exclude all charts with names matching one or more of the supplied regular expressions. All other charts will be included.
- Data Model Pattern (Optional): Use it to control whether to include data modes as part of metadata ingestion.
- Include: Explicitly include data models by adding a list of comma-separated regular expressions to the ‘Include’ field. OpenMetadata will include all data models with names matching one or more of the supplied regular expressions. All other data models will be excluded.
- Exclude: Explicitly exclude data models by adding a list of comma-separated regular expressions to the ‘Exclude’ field. OpenMetadata will exclude all data models with names matching one or more of the supplied regular expressions. All other data models will be included.
- Database Service Name (Optional): Enter the name of Database Service which is already ingested in OpenMetadata to create lineage between dashboards and database tables.
- Enable Debug Log (toggle): Set the ‘Enable Debug Log’ toggle to set the default log level to debug.
- Include Owners (toggle): Set the ‘Include Owners’ toggle to control whether to include owners to the ingested entity if the owner email matches with a user stored in the OM server as part of metadata ingestion. If the ingested entity already exists and has an owner, the owner will not be overwritten.
- Include Tags (toggle): Set the ‘Include Tags’ toggle to control whether to include tags in metadata ingestion.
- Include Data Models (toggle): Set the ‘Include Data Models’ toggle to control whether to include tags as part of metadata ingestion.
- Mark Deleted Dashboards (toggle): Set the ‘Mark Deleted Dashboards’ toggle to flag dashboards as soft-deleted if they are not present anymore in the source system.
- Include Draft Dashboard (toggle): Set the ‘Include Draft Dashboard’ toggle to include draft dashboards. By default it will include draft dashboards.
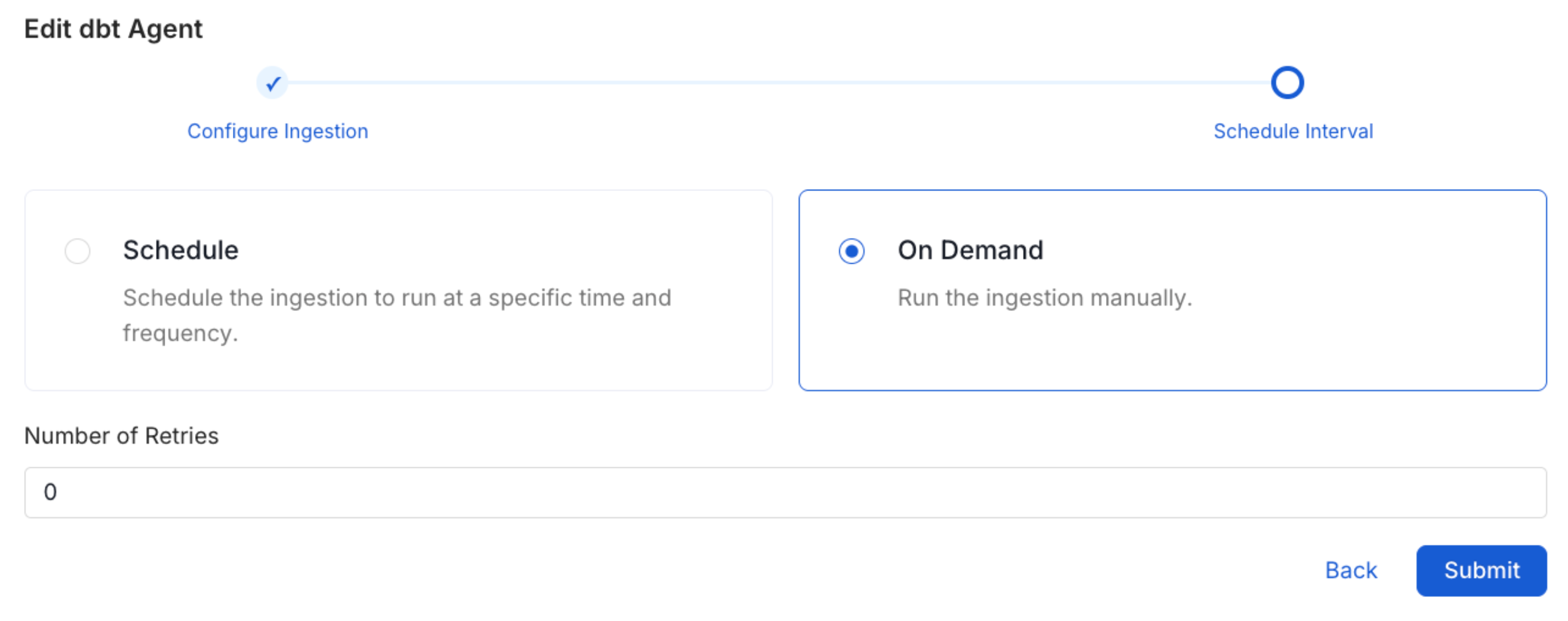
Schedule the Ingestion and Deploy
Scheduling can be set up at an hourly, daily, weekly, or manual cadence. The
timezone is in UTC. Select a Start Date to schedule for ingestion. It is
optional to add an End Date.Review your configuration settings. If they match what you intended,
click Deploy to create the service and schedule metadata ingestion.If something doesn’t look right, click the Back button to return to the
appropriate step and change the settings as needed.After configuring the workflow, you can click on Deploy to create the
pipeline.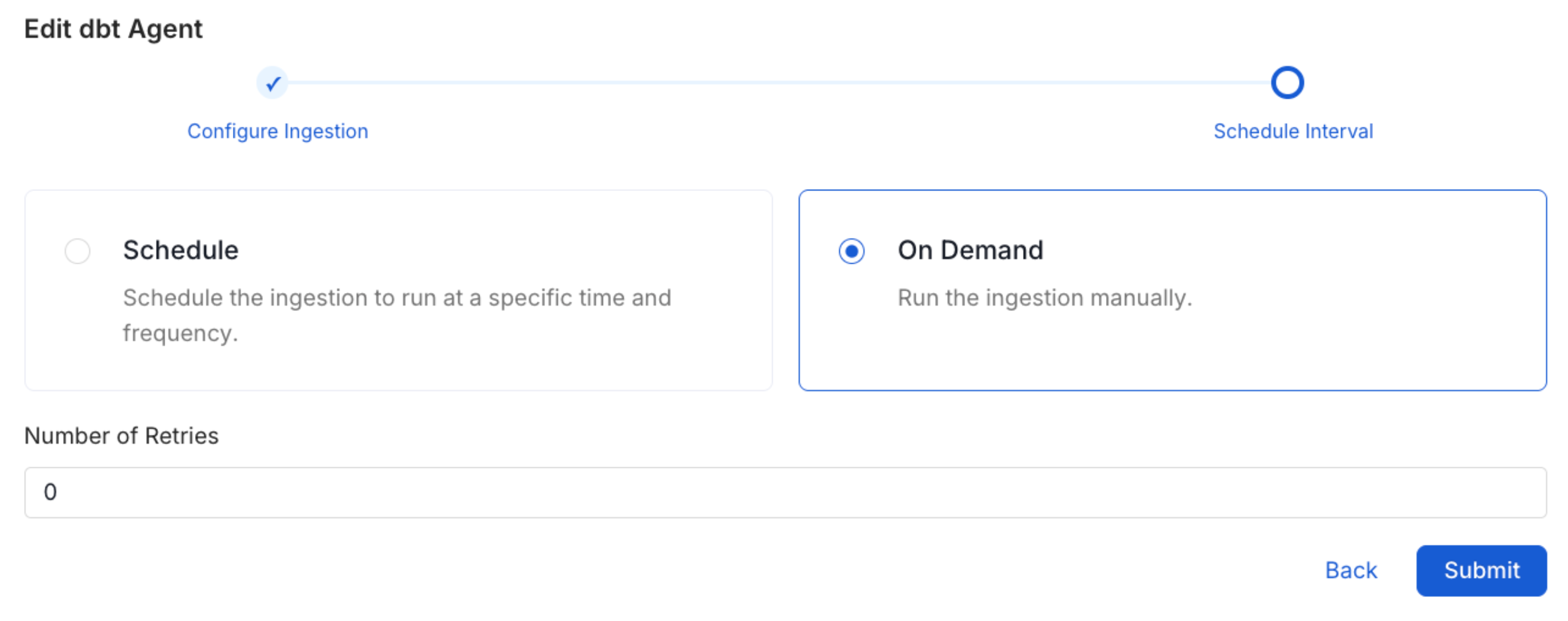
Securing Superset Connection with SSL in OpenMetadata
- To establish secure connections between OpenMetadata and Superset, navigate to the
Advanced Configsection. We need to update theCertificate Pathand ensure that the certificates are accessible from the Airflow Server.
- To establish secure connections between OpenMetadata and Superset’s MySQL database, you need to configure SSL certificates appropriately. If you only require SSL validation, specify the
caCertificateto use the CA certificate for validating the server’s certificate. For mutual authentication, where both client and server need to authenticate each other, you must provide all three parameters:ssl_keyfor the client’s private key,ssl_certfor the client’s SSL certificate, andssl_cafor the CA certificate to validate the server’s certificate.
- To establish secure connections between OpenMetadata and Superset’s PostgreSQL database, you can configure SSL using different SSL modes provided by PostgreSQL, each offering varying levels of security.Under
PostgresConnection Advanced Config, specify the SSL mode appropriate for your connection, such asprefer,verify-ca,allow, and others. After selecting the SSL mode, provide the CA certificate used for SSL validation (caCertificate). Note that PostgreSQL requires only the CA certificate for SSL validation.
Lineage
To establish lineage from your database tables to dashboards, you must add the corresponding database service name.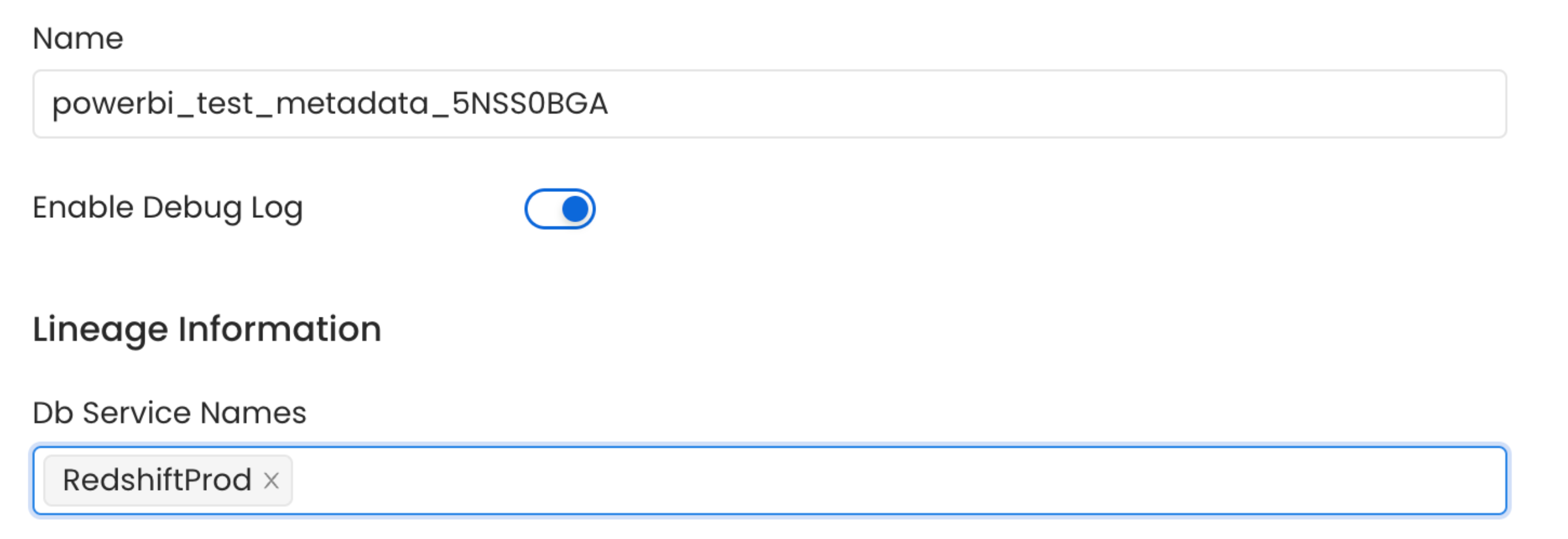
Troubleshooting
Superset Troubleshooting
Learn more about how to troubleshoot common Superset connector issues and resolve configuration or ingestion errors.