Requirements
To extract metadata using the Cassandra connector, ensure the user in the connection has the following permissions:- Read Permissions: The ability to query tables and perform data extraction.
- Schema Operations: Access to list and describe keyspaces and tables.
Metadata Ingestion
Connection Details
Connection Details
- Username: Username to connect to Cassandra. This user must have the necessary permissions to perform metadata extraction and table queries.
- Host Port: When using the
cassandraconnecion schema, the hostPort parameter specifies the host and port of the Cassandra. This should be specified as a string in the formathostname:port. E.g.,localhost:9042.- databaseName: Optional name to give to the database in OpenMetadata. If left blank, we will use default as the database name. Auth Type: Following authentication types are supported:
- Basic Authentication: We’ll use the user credentials to connect to Cassandra
- password: Password of the user.
- DataStax Astra DB Configuration: Configuration for connecting to DataStax Astra DB in the cloud.
- connectTimeout: Timeout in seconds for establishing new connections to Cassandra.
- requestTimeout: Timeout in seconds for individual Cassandra requests.
- token: The Astra DB application token used for authentication.
- secureConnectBundle: File path to the Secure Connect Bundle (.zip) used for a secure connection to DataStax Astra DB. SSL Modes There are a couple of types of SSL modes that Cassandra supports which can be added to ConnectionArguments, they are as follows:
- disable: SSL is disabled and the connection is not encrypted.
- allow: SSL is used if the server requires it.
- prefer: SSL is used if the server supports it.
- require: SSL is required.
- verify-ca: SSL must be used and the server certificate must be verified.
- verify-full: SSL must be used. The server certificate must be verified, and the server hostname must match the hostname attribute on the certificate. SSL Configuration In order to integrate SSL in the Metadata Ingestion Config, the user will have to add the SSL config under sslConfig which is placed in the source.
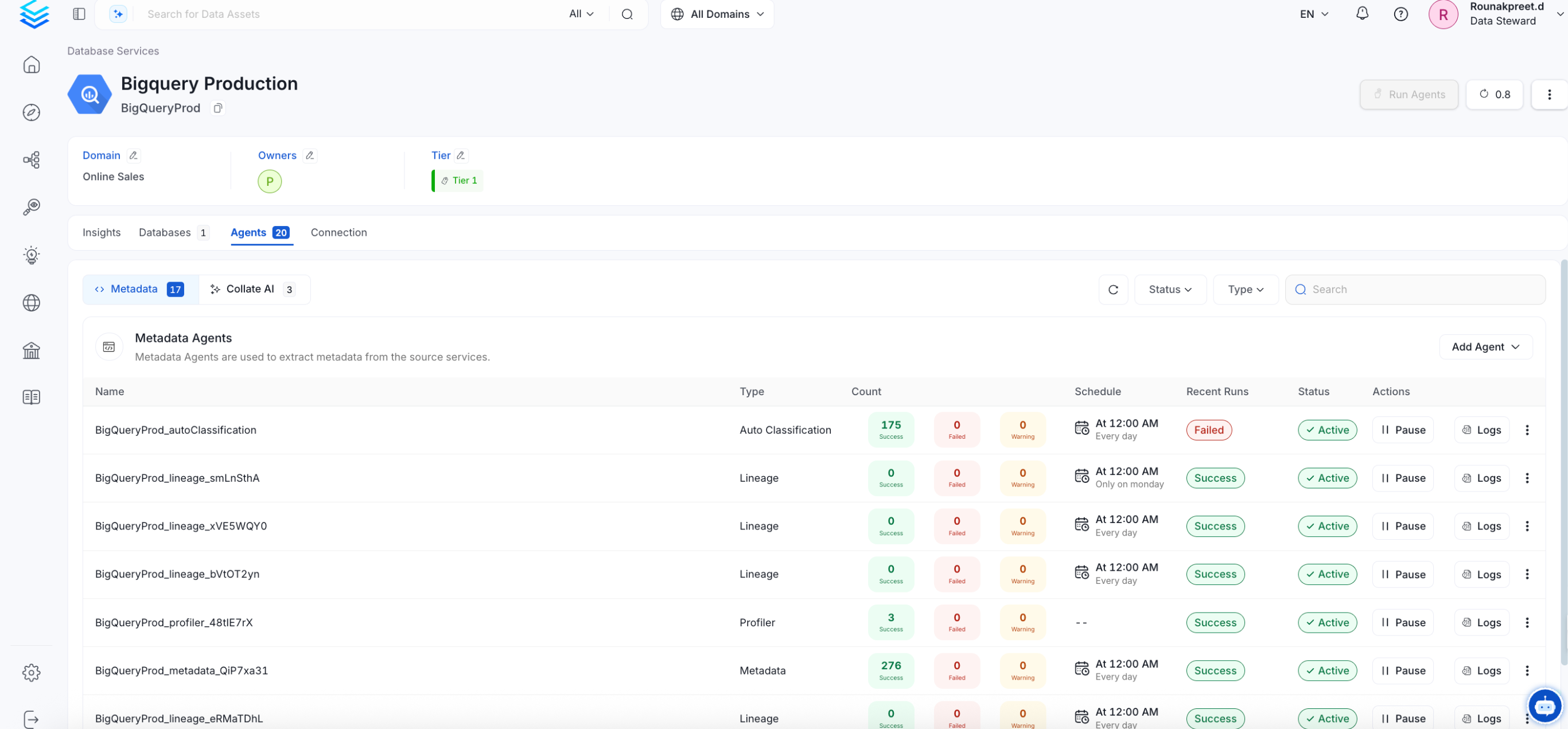
Test the Connection
Once the credentials have been added, click on Test Connection and Save the changes.
Configure Metadata Ingestion
In this step we will configure the metadata ingestion pipeline,
Please follow the instructions below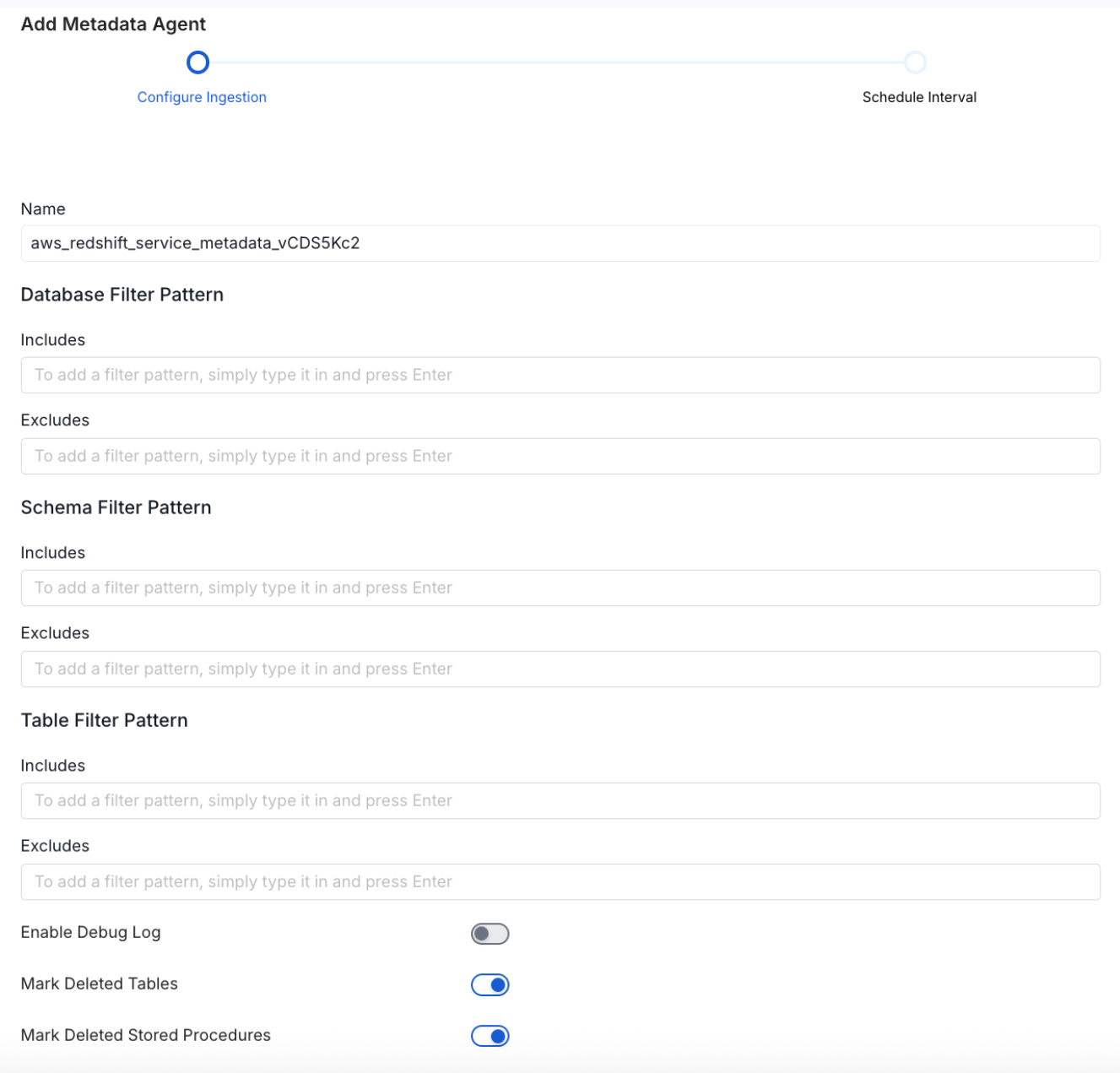
Metadata Ingestion Options
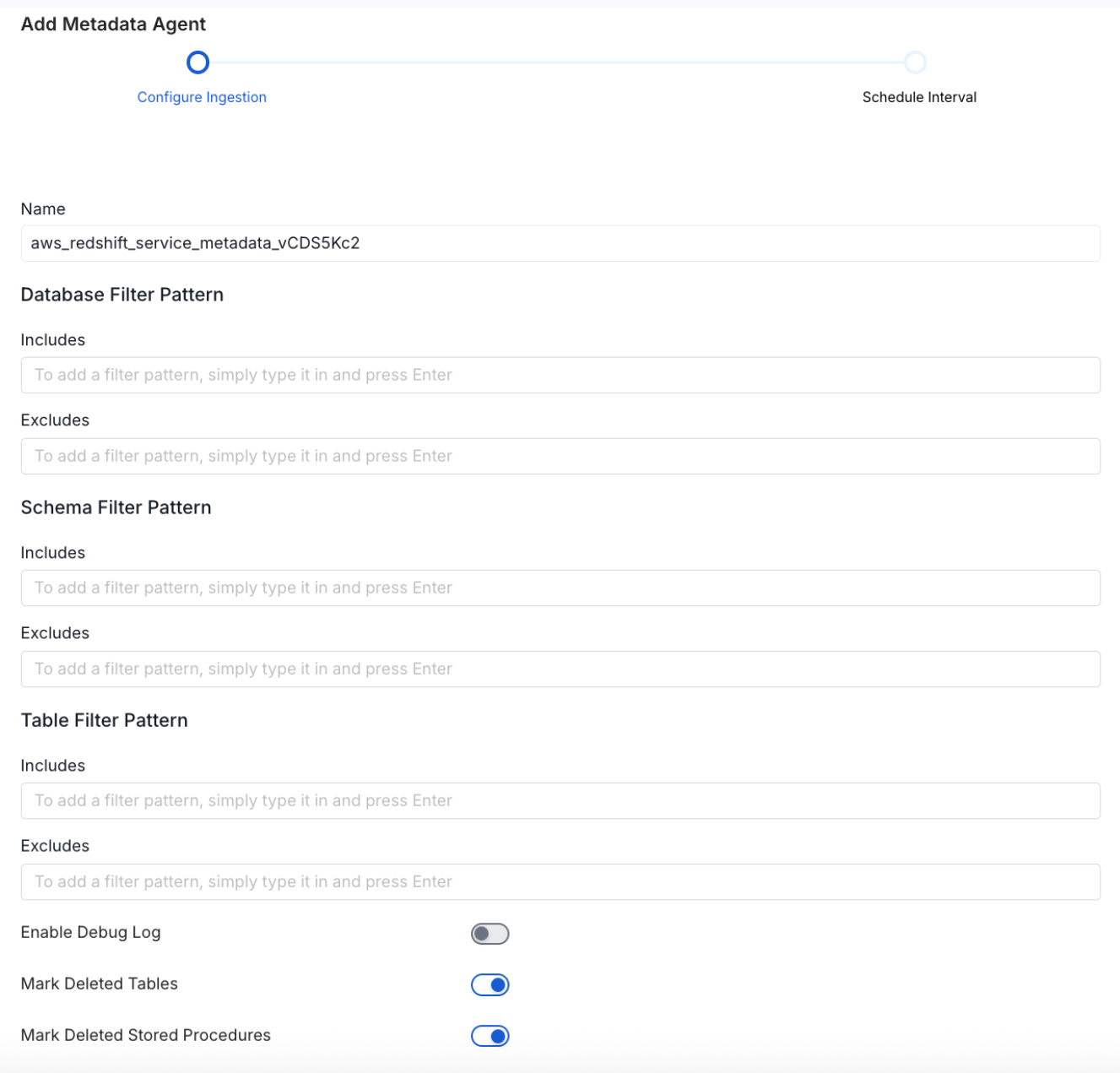
- Name: This field refers to the name of ingestion pipeline, you can customize the name or use the generated name.
-
Database Filter Pattern (Optional): Use to database filter patterns to control whether or not to include database as part of metadata ingestion.
- Include: Explicitly include databases by adding a list of comma-separated regular expressions to the Include field. OpenMetadata will include all databases with names matching one or more of the supplied regular expressions. All other databases will be excluded.
- Exclude: Explicitly exclude databases by adding a list of comma-separated regular expressions to the Exclude field. OpenMetadata will exclude all databases with names matching one or more of the supplied regular expressions. All other databases will be included.
-
Schema Filter Pattern (Optional): Use to schema filter patterns to control whether to include schemas as part of metadata ingestion.
- Include: Explicitly include schemas by adding a list of comma-separated regular expressions to the Include field. OpenMetadata will include all schemas with names matching one or more of the supplied regular expressions. All other schemas will be excluded.
- Exclude: Explicitly exclude schemas by adding a list of comma-separated regular expressions to the Exclude field. OpenMetadata will exclude all schemas with names matching one or more of the supplied regular expressions. All other schemas will be included.
-
Table Filter Pattern (Optional): Use to table filter patterns to control whether to include tables as part of metadata ingestion.
- Include: Explicitly include tables by adding a list of comma-separated regular expressions to the Include field. OpenMetadata will include all tables with names matching one or more of the supplied regular expressions. All other tables will be excluded.
- Exclude: Explicitly exclude tables by adding a list of comma-separated regular expressions to the Exclude field. OpenMetadata will exclude all tables with names matching one or more of the supplied regular expressions. All other tables will be included.
- Enable Debug Log (toggle): Set the Enable Debug Log toggle to set the default log level to debug.
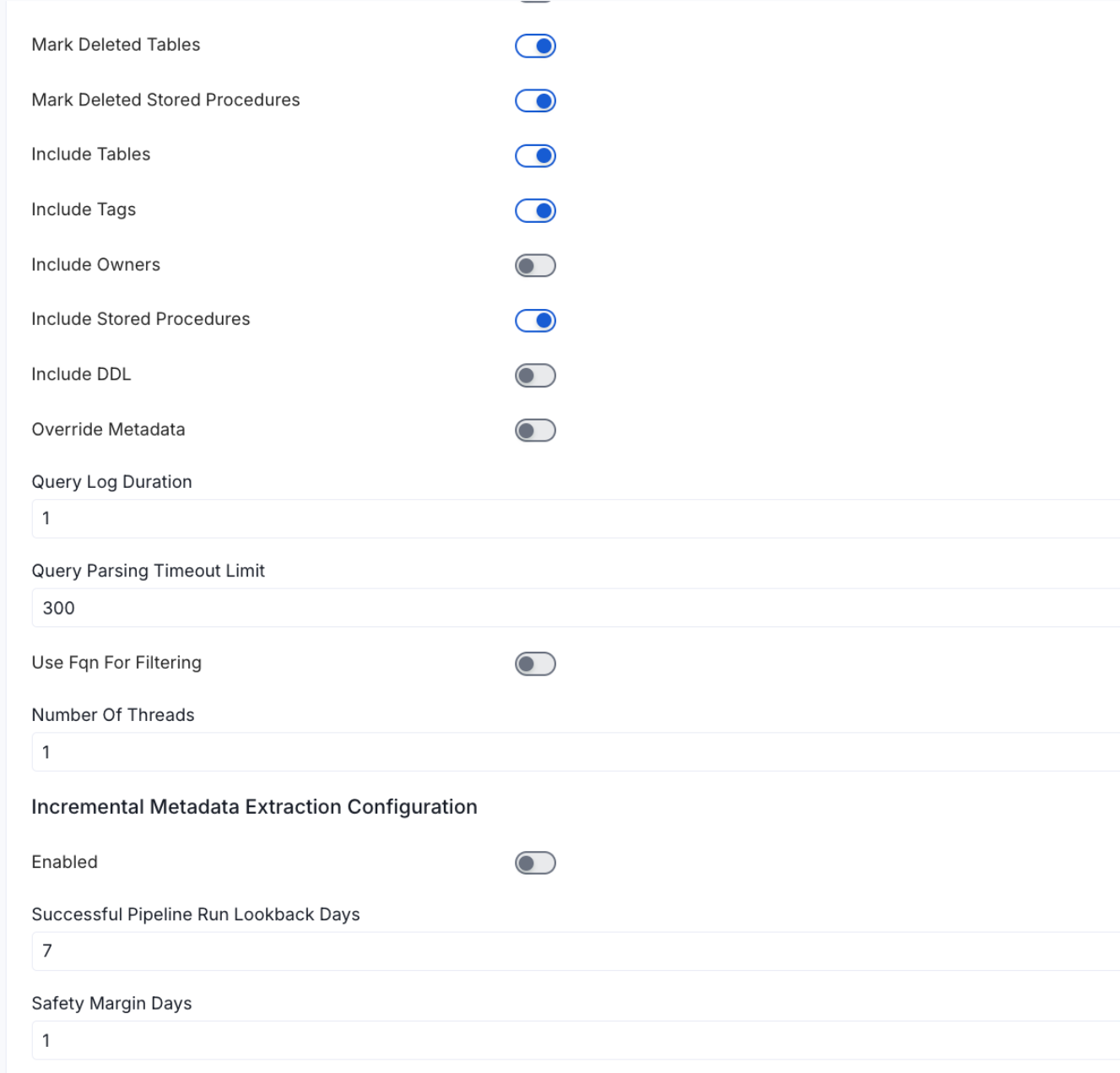
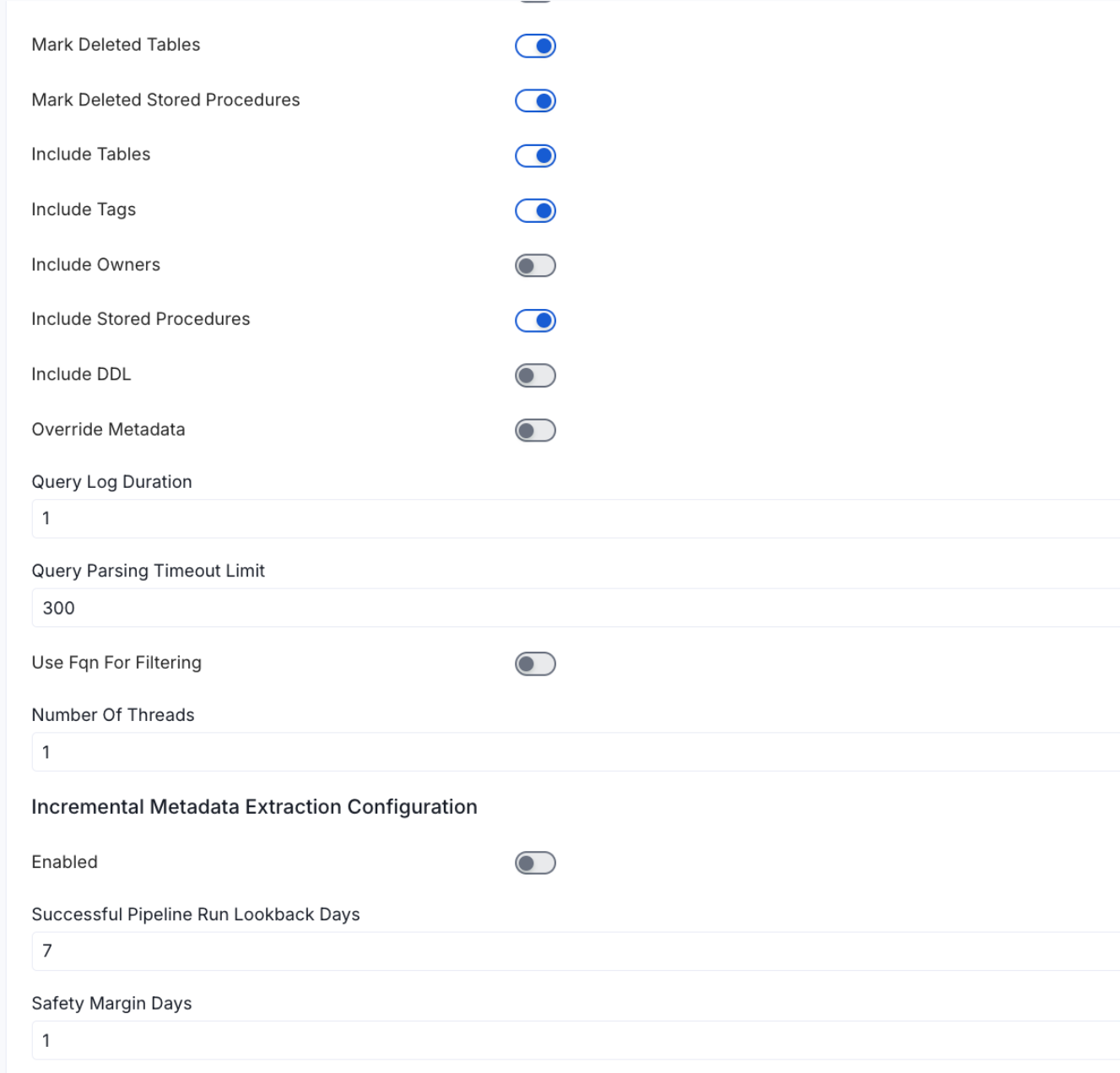
- Mark Deleted Tables (toggle): Set the Mark Deleted Tables toggle to flag tables as soft-deleted if they are not present anymore in the source system.
- Mark Deleted Tables from Filter Only (toggle): Set the Mark Deleted Tables from Filter Only toggle to flag tables as soft-deleted if they are not present anymore within the filtered schema or database only. This flag is useful when you have more than one ingestion pipelines. For example if you have a schema
- includeTables (toggle): Optional configuration to turn off fetching metadata for tables.
- includeViews (toggle): Set the Include views toggle to control whether to include views as part of metadata ingestion.
- includeTags (toggle): Set the ‘Include Tags’ toggle to control whether to include tags as part of metadata ingestion.
- includeOwners (toggle): Set the ‘Include Owners’ toggle to control whether to include owners to the ingested entity if the owner email matches with a user stored in the OM server as part of metadata ingestion. If the ingested entity already exists and has an owner, the owner will not be overwritten.
- includeStoredProcedures (toggle): Optional configuration to toggle the Stored Procedures ingestion.
- includeDDL (toggle): Optional configuration to toggle the DDL Statements ingestion.
- queryLogDuration (Optional): Configuration to tune how far we want to look back in query logs to process Stored Procedures results.
- queryParsingTimeoutLimit (Optional): Configuration to set the timeout for parsing the query in seconds.
- useFqnForFiltering (toggle): Regex will be applied on fully qualified name (e.g service_name.db_name.schema_name.table_name) instead of raw name (e.g. table_name).
-
Incremental (Beta): Use Incremental Metadata Extraction after the first execution. This is done by getting the changed tables instead of all of them. Only Available for BigQuery, Redshift and Snowflake
- Enabled: If
True, enables Metadata Extraction to be Incremental. - lookback Days: Number of days to search back for a successful pipeline run. The timestamp of the last found successful pipeline run will be used as a base to search for updated entities.
- Safety Margin Days: Number of days to add to the last successful pipeline run timestamp to search for updated entities.
- Enabled: If
- Threads (Beta): Use a Multithread approach for Metadata Extraction. You can define here the number of threads you would like to run concurrently.
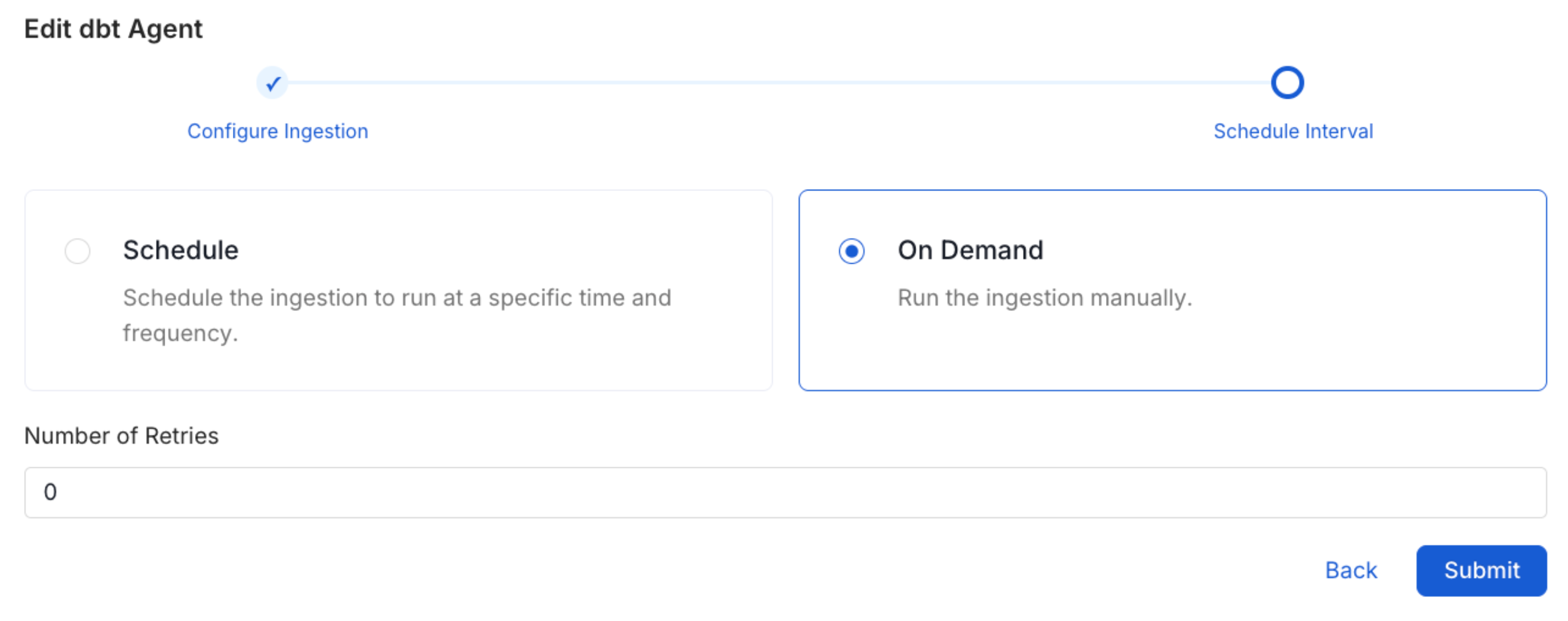
Schedule the Ingestion and Deploy
Scheduling can be set up at an hourly, daily, weekly, or manual cadence. The
timezone is in UTC. Select a Start Date to schedule for ingestion. It is
optional to add an End Date.Review your configuration settings. If they match what you intended,
click Deploy to create the service and schedule metadata ingestion.If something doesn’t look right, click the Back button to return to the
appropriate step and change the settings as needed.After configuring the workflow, you can click on Deploy to create the
pipeline.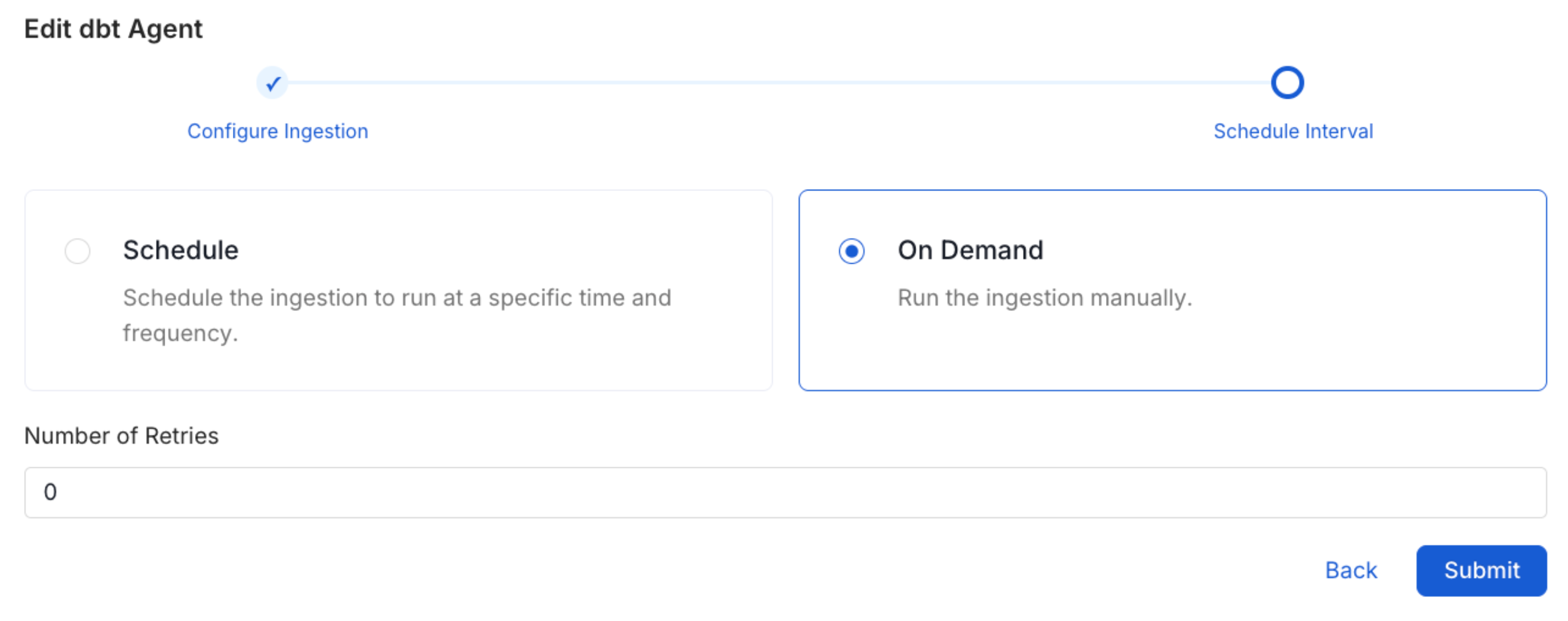
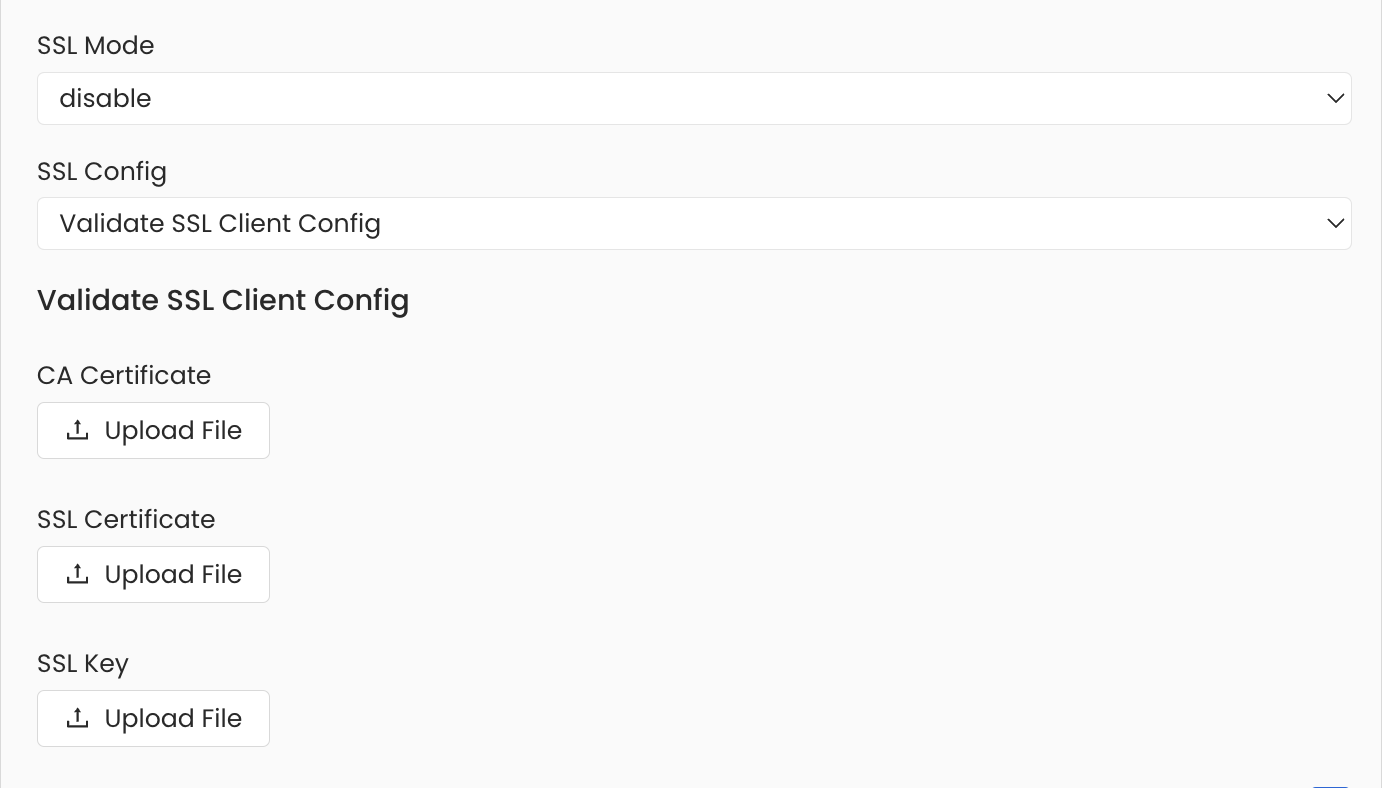
Securing Cassandra Connection with SSL in OpenMetadata
To establish secure connections between OpenMetadata and a Cassandra database, you can use any SSL mode provided by Cassandra, except disable. UnderAdvanced Config, after selecting the SSL mode, provide the CA certificate, SSL certificate and SSL key.
Troubleshooting
Related
Usage Workflow
Learn more about how to configure the Usage Workflow to ingest Query information from the UI.
Lineage Workflow
Learn more about how to configure the Lineage from the UI.
Profiler Workflow
Learn more about how to configure the Data Profiler from the UI.
Data Quality Workflow
Learn more about how to configure the Data Quality tests from the UI.
dbt Integration
Learn more about how to ingest dbt models’ definitions and their lineage.